
In Cayman: Anton Livaja
This conversation isn’t really about music, AI, or crypto. It’s about what happens when you stop assuming things work...

Cybersecurity, Sovereignty & Bitcoin
Anton Livaja has spent years protecting billions in digital assets, advising Bitcoin companies, and helping people ta...

Fighting Back Against Crypto and Supply Chain Threats
In this insightful discussion, host Jim Love is joined by Anton Livaja, co-founder of Distrust, to uncover how advanc...
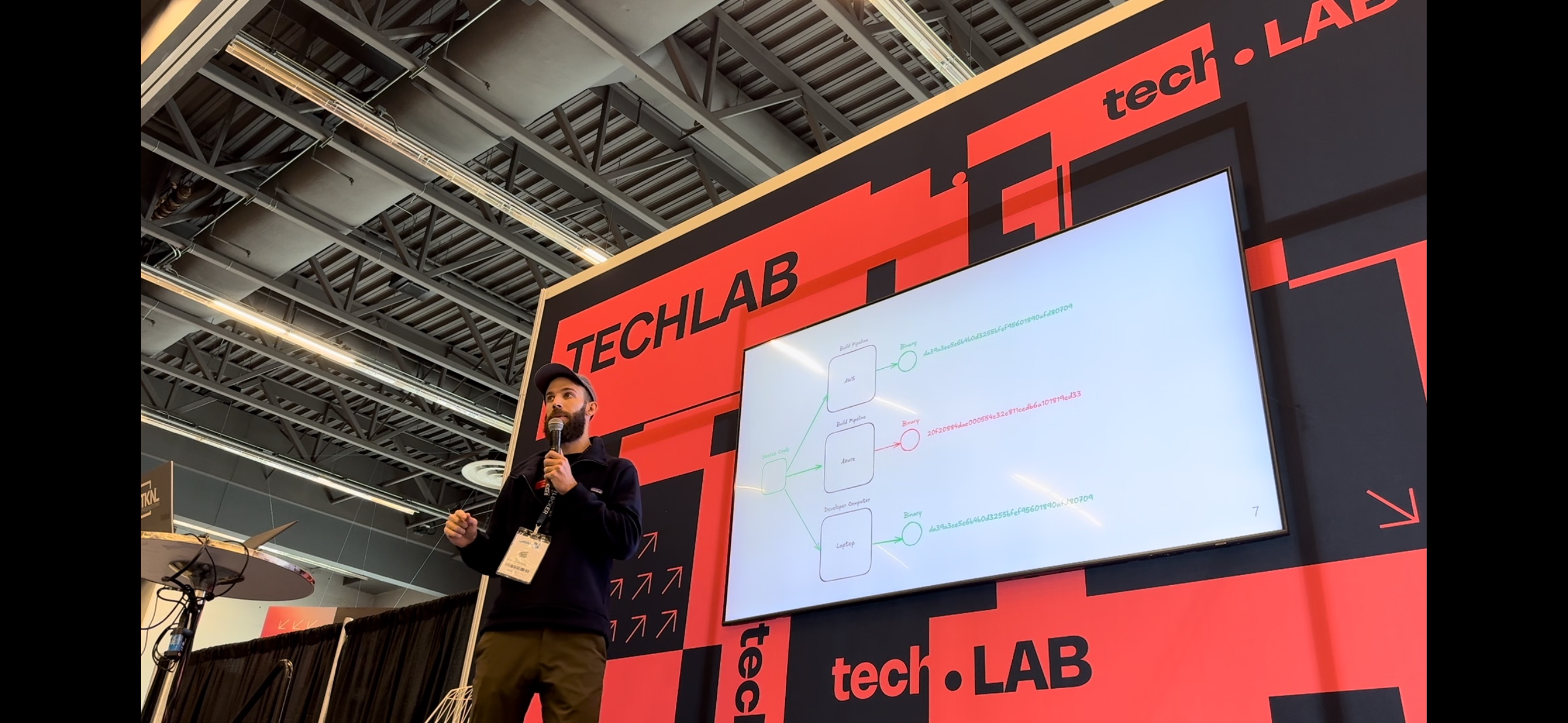
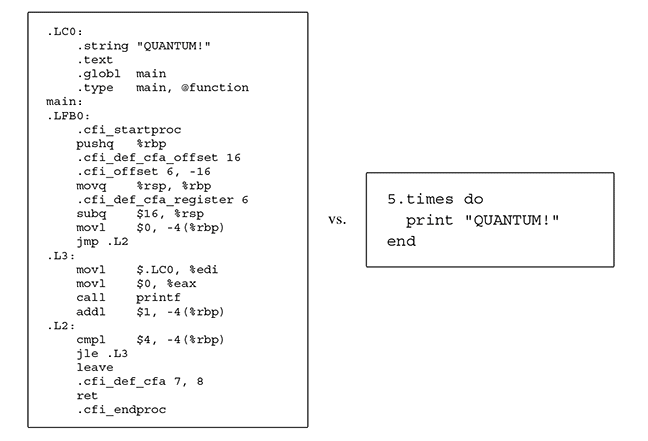
Expanding (Dis)Trust - talk about compiler safety, determinism and StageX
This talk which was held in Montreal at the InCyber conference taking place Oct 29-30 2024, covers topics regarding b...

Protecting Your Digital Life and Bitcoin
On this episode of Your Life, Your Terms podcast, Anthony and I dive into some best practices around personal securit...

AI and Social Engineering
Imagine the following scenario. You are the financial controller of a company, and receive a late night call to join ...

Elevating Data Security
The modern regulatory landscape frequently mandates the collection and retention of Personally Identifiable Informati...

Nostrica Nostr Relay Panel
On this Nostrica panel we talk about Nostr relays, and their future.
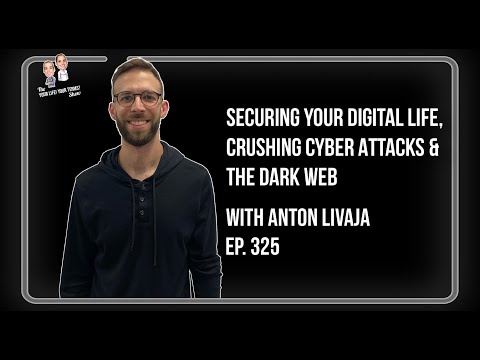
Crushing Cyber Attacks & The Dark Web
On this episode of Your Life, Your Terms podcast, Anthony, Tom and I dive into some best practices around staying saf...

Two Factor Authentication (2FA)
If you haven’t read I Have a Password System, and don’t feel confident with how you manage your passwords, it’s recom...
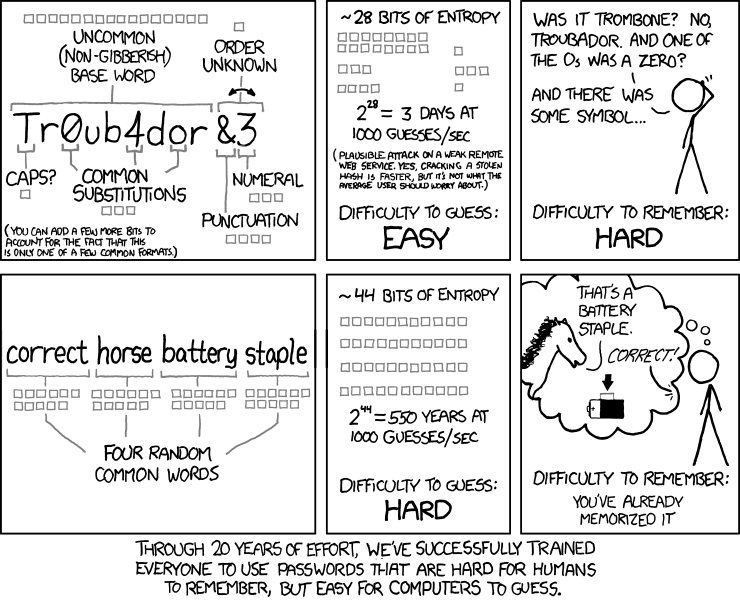
I Have a Password System
Even though passwords are one of the most common and basic types of security mechanisms, few understand what makes a ...
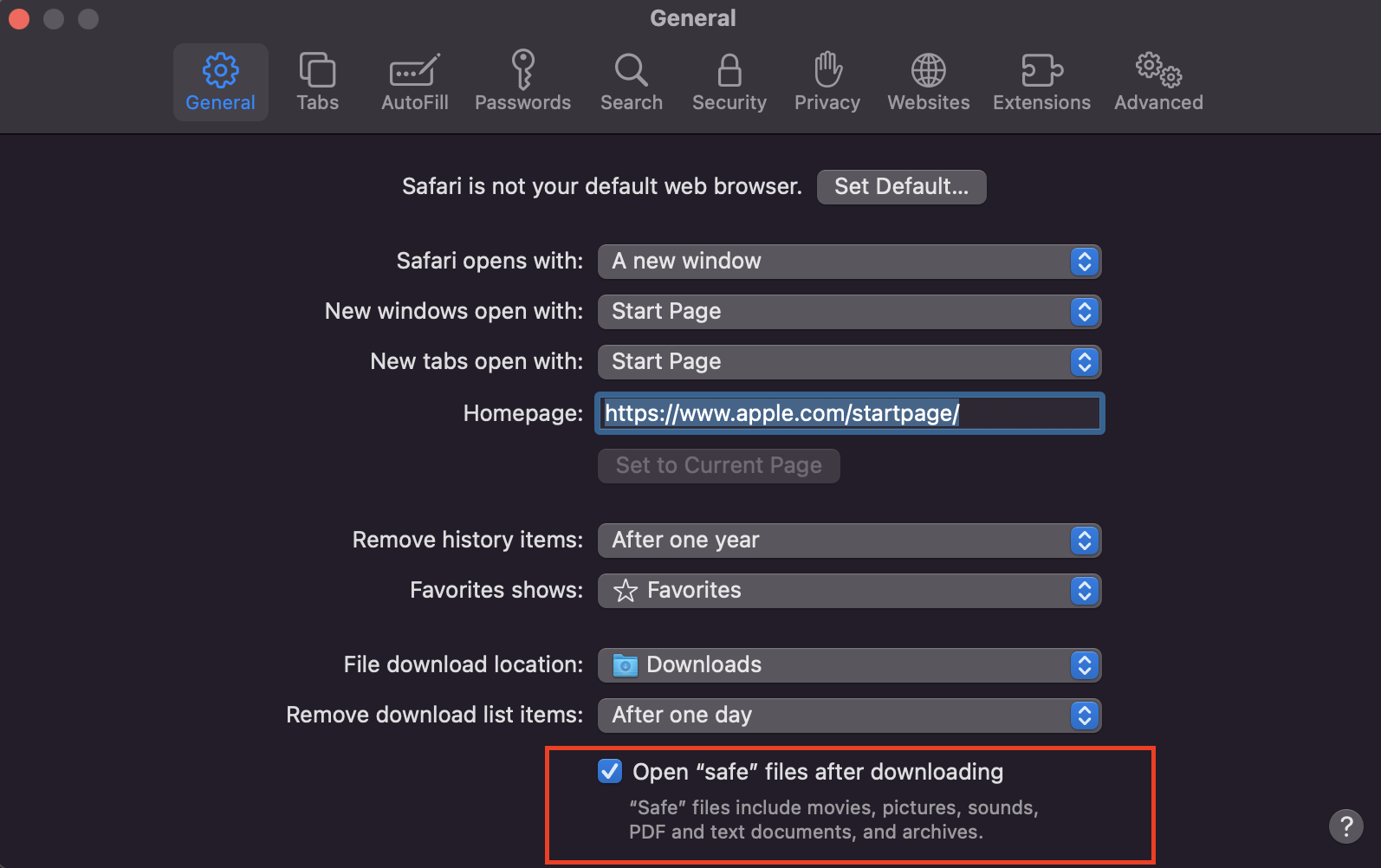
Can Clicking a Link Get You Hacked?
How much damage can a malicious actor do by getting someone to click on a link? This blog focuses on exploring the di...
Why Visual Programming Doesn't Suck
I’m here to tell you that visual programming, and diagrammatic reasoning in particular, is a formidable tool-set if u...